On March 30, 2026, someone hijacked one of the most widely used JavaScript packages on the internet. And with a single npm install, backdoors were deployed on tens of thousands of machines.
The package was Axios. Over 100 million weekly downloads. If you've built anything in JavaScript over the past decade, you've almost certainly used this HTTP library. The attacker didn't change a single line of Axios's source code. Instead, they compromised the maintainer's account, added a fake package that had been created just hours earlier as a dependency, and pushed an update. The moment that fake package installed, it detected the OS, downloaded a custom remote access trojan (RAT), executed it, and deleted itself. By the time you checked your node_modules folder, it was already gone.
What happened?
This is a software supply chain attack. Not an attack on your code, but an attack on the packages your code depends on.
Here's how this one played out.
- Maintainer account compromised
The attacker hijacked the Axios npm maintainer's account. It's believed a long-used npm token was leaked. - Fake package pre-staged
39 minutes before the attack, they registered a malicious package calledplain-crypto-js@4.2.1on npm. It was a clone of the legitimate crypto-js with a malicious postinstall script injected. - Axios update pushed
Using the compromised account, they publishedaxios@1.14.1andaxios@0.30.4, adding plain-crypto-js to the dependency list. No GitHub tag, no release notes — a ghost update. - Auto-infection
Any project using Axios with^1.14.0range would automatically pull 1.14.1 onnpm install, triggering the plain-crypto-js postinstall script. - Platform-specific RAT deployment
On macOS, it disguised itself as an Apple system daemon. On Windows, it copied PowerShell as wt.exe to bypass EDR. On Linux, it ran a Python script. - Evidence destruction
The malicious script (setup.js) was deleted and replaced with a clean package.json with no postinstall hook. Post-mortem inspection of node_modules would show a perfectly normal-looking package.
Google Threat Intelligence attributed this attack to North Korea-linked threat actor UNC1069. Across 135 endpoints monitored by security firm Huntress, the malware connected to the attacker's server in just 89 seconds after installation.
This isn't just about Axios
The TeamPCP campaign that same quarter was even worse. After compromising Trivy's GitHub Actions token, a self-replicating worm (CanisterWorm) spread across 66+ npm packages. Within 8 days, it contaminated 5 ecosystems: GitHub Actions, Docker Hub, npm, PyPI, and VS Code Marketplace.
Why is this different now?
Supply chain attacks aren't new. SolarWinds (2020), Log4Shell (2021), XZ Utils (2024) — you've heard these stories. But two things have changed simultaneously.
| Traditional supply chain attacks | AI agent era supply chain attacks | |
|---|---|---|
| Attack prep time | Months to years (XZ Utils: 2 years of trust-building) | Hours to days (Axios: completed in 39 minutes) |
| Spread | Single package, single ecosystem | Auto-propagating, 5 ecosystems infected simultaneously |
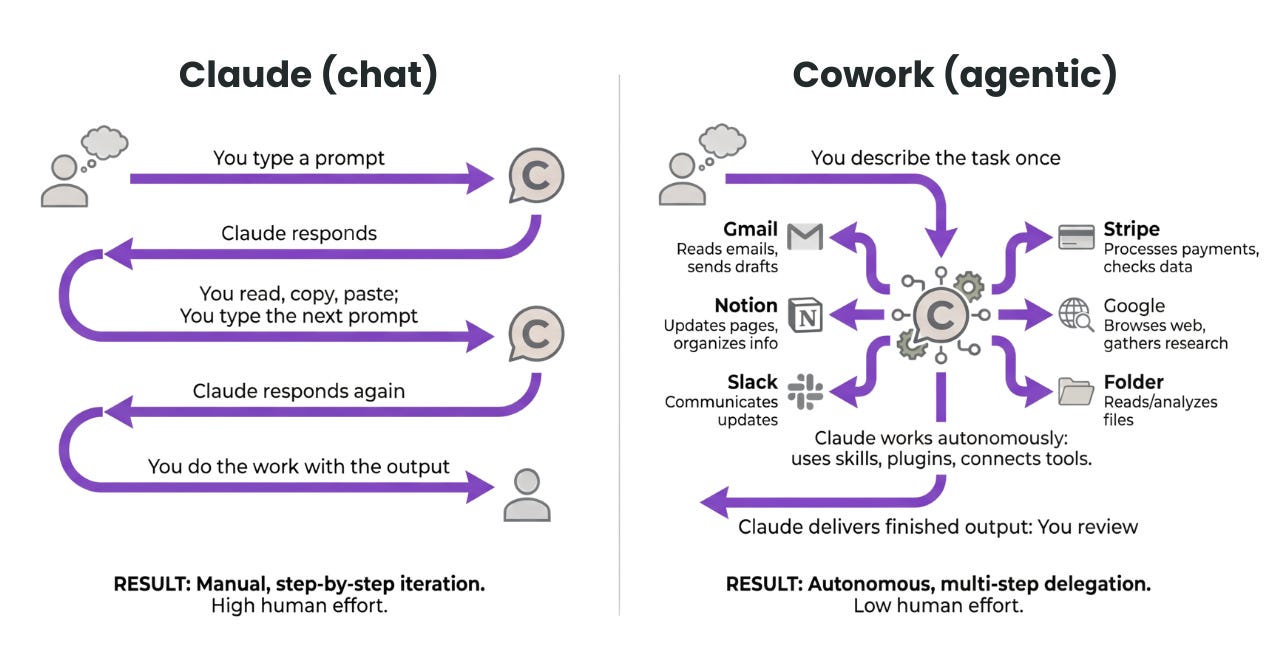
| Who decides on dependencies | Developers review manually | AI agents auto-install, review time approaches 0 |
| Detection method | CVE database matching (npm audit) | Behavioral analysis needed (new malware with no CVE) |
| Industry avg detection time | 267 days (SolarWinds: 14 months) | Socket: detected in 6 minutes (63,000x faster) |
| Time to damage after infection | Days to weeks | 89 seconds (install to C2 connection) |
a16z sums up the core problem: "The attack surface is expanding faster than humans can monitor, and the entity making dependency decisions is increasingly not human."
3 ways AI agents amplify the risk
1. They pick vulnerable versions more often
An analysis of 117,000 dependency changes found that AI agents select known vulnerable versions 50% more often than humans. And those vulnerable versions tend to require major upgrades to fix.
2. They recommend packages that don't exist (slopsquatting)
About 20% of packages LLMs recommend don't actually exist. Attackers exploit this by pre-registering names that AI repeatedly suggests, then planting malware. One researcher uploaded dummy packages using this method and got 30,000 downloads in weeks — mostly from AI-automated workflows.
3. Autonomous agents optimize for "does it work," not "is it safe"
Production-deployed autonomous coding agents handle dependency installation, build execution, and PR creation with zero human intervention. Their optimization target is "does it run?" — not "is it secure?" Security review time effectively compresses to zero.
How to protect yourself
Whether you use AI agents or code by hand, supply chain security is no longer optional. Here's what you can do right now.
- Enforce lockfile-based installs
Usenpm cias your default. Unlikenpm install, it only installs exact versions specified in your lockfile. If your CI/CD pipeline still runsnpm install, switch immediately. - Adopt behavioral analysis security tools
Go beyondnpm audit(which only checks CVE databases) and use tools that analyze what packages actually do. Socket (detects network access, shell execution, env var reads) and Oligo (runtime behavior monitoring) are leading options. - Restrict AI agent permissions
Require human approval when autonomous coding agents add dependencies. Enable features like Claude Code's--permission-prompt-toolor Cursor's dependency installation confirmation prompts. - Minimize dependency ranges
Replace caret ranges like^1.14.0with exact versions (1.14.0), or use Renovate/Dependabot for managed updates. New versions won't auto-install. - Block postinstall scripts
Setnpm config set ignore-scripts trueto block auto-execution scripts during package installation. The Axios malware executed via a postinstall hook. Whitelist only the scripts you actually need. - Run regular dependency audits
Use tools likenpx socket optimizeto periodically scan your project's transitive dependencies. Out of the average JS project's 755 transitive dependencies, only a tiny fraction were chosen by your team.
Think you might already be infected?
Search your lockfile for axios@1.14.1, axios@0.30.4, and plain-crypto-js@4.2.1. If found, roll back to a safe version immediately. Check for: macOS /Library/Caches/com.apple.act.mond, Windows %PROGRAMDATA%\wt.exe, Linux /tmp/ld.py.